All blog posts
Page 12 of 53
-
Fastly Named to Newsweek Excellence Index 2025
Fastly's inclusion in the 2025 Newsweek Excellence Index reflects our dedication to social responsibility and employee well-being, showcasing our commitment to excellence.

-
2024: End of Year Product Release Rewind
We’re always improving the Fastly platform to enable developers, security experts, and more! See an overview of the product releases that we unveiled in 2024.

-
What does it all mean? An introduction to semantic caching and Fastly’s AI Accelerator
Fastly’s AI Accelerator is a pass-through API that makes semantic caching easy and works with your existing code.

-
How to Save Christmas for Beyoncé
This Christmas, Netflix is bringing the world a Beyoncé halftime show, promising unforgettable moments - but will this massive live event go off without a hitch?

-
Build, Store, and Scale: Fastly Object Storage With Zero Egress Costs is Here
Tired of high storage bills? Fastly Object Storage offers always-free egress and straightforward pricing, empowering your innovation without breaking the bank.

-
Start your next Fastly Compute JavaScript application with npm init
If you're using Fastly Compute, the `npm init` script makes it easy to set up your projects with familiar tools.
-
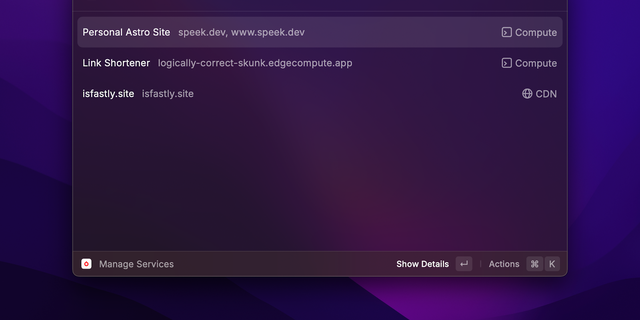
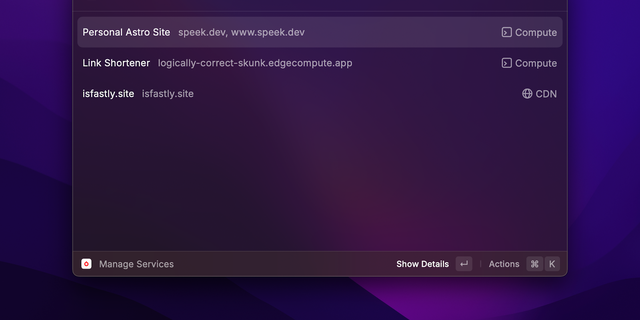
Introducing the Fastly Extension for Raycast
Introducing the Fastly extension for Raycast on macOS! Simplify your service management, get support, and find essential resources all in one place.
-
The History of DDoS
Discover the impact of DDoS attacks on businesses. Learn how these disruptions can lead to financial losses, damaged reputations, and the importance of prevention.
-
Navigating the Challenges of Online Live Streaming
Join us as we delve into the realities of live event streaming, highlighting the lessons learned from disruptions and our commitment to delivering reliable viewer experiences.
-
Fastly Achieves AWS Retail Competency Status
Fastly has achieved Amazon Web Services (AWS) Retail Competency status! This achievement recognizes Fastly as a distinguished member of the AWS Partner Network (APN).
-
Fastly named a Leader in the IDC MarketScape: Worldwide Edge Delivery Services 2024
Celebrating our recognition as a Leader in the IDC MarketScape: Worldwide Edge Delivery Services 2024, Fastly remains dedicated to empowering developers with cutting-edge solutions.
-
Streamline Your Logging with Grafana Integration
Enhance your business performance with Fastly's Real-Time Log Streaming, now supporting Grafana Cloud for effortless log storage and insightful analysis.
-
Speeding up JavaScript on Compute
Discover how Fastly enhances JavaScript performance with our advanced compiler optimizations, achieving a remarkable 3x speedup for developers.
-
What Fastly saw on election night
Learn how voter fatigue and alternative media are changing public engagement with politics and how that impacted election night in the U.S..
-
War story: RPKI is working as intended
Explore the transformative impact of RPKI on the Internet. Discover how collaboration and perseverance drive fundamental changes in routing reliability and security.
-
2024 US Elections Threat Landscape
With the election nearing, businesses face heightened risks from cybercriminals. Discover strategies to safeguard against phishing, DDoS attacks, and data theft.
-
Battleground states: News media traffic during the 2024 election debates
This blog describes the aggregated traffic in the seven states to news media outlets during the presidential and VP debates.
-
Introducing Log Explorer & Insights: Actionable data at your fingertips
Introducing Log Explorer & Insights, which unlocks valuable insights within your log data to drive informed decisions and identify opportunities for optimization and innovation.
-
OpenJS Foundation and Fastly Announce Strategic Collaboration to Support the Evolution of the JavaScript Ecosystem
The OpenJS Foundation is excited to announce a strategic partnership with Fastly, to enhance the performance, security, and scalability of JavaScript projects across the globe.
-
Building a better application DDoS solution
Fastly DDoS Protection offers rapid deployment and automatic defense against DDoS threats, helping maintain the performance of your applications and APIs in a volatile digital landscape.